July 14th: as Microsoft flag a ‘Critical’ Level-10 DNS vulnerability on Domain Name System (DNS) servers worldwide, Lineal engineers rush to patch the infrastructure of dozens of organisations overnight.
The Microsoft Security Response Center recently released details of CVE-2020-135, a ‘Critical Remote Code Execution’ weakness deemed ‘wormable’ (potentially spreading between devices automatically) affecting all Windows Server versions.
A grade of 10.0 is the highest possible severity level that can be assigned under the Common Vulnerability Scoring System Calculator. For comparison the WannaCry attack, which temporarily crippled the NHS in 2017, had a CVSS rating of 8.5.
Lineal staff use remote monitoring software to administer large numbers of client servers and devices, monitor hardware health and deploy patches more rapidly – and were quickly on the case overnight to patch the vulnerability as a special emergency.
Within 8 hours we’d patched a large number of DNS servers – applying both an initial fix and further scheduled updates.
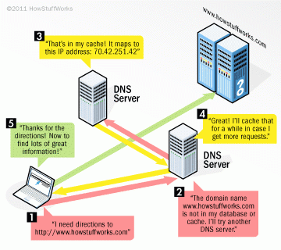
DNS is a naming technology which translates the identities of computers, servers and other networked devices into the IP addresses used for connecting on private and public IT networks.
For this reason, DNS servers often have massive reach, and must be carefully protected to mitigate the risk of compromising an organisation’s technology on a huge scale – even across the globe.
Israeli IT security firm Checkpoint Software Technologies, who discovered the 17-year old hidden bug and reported it to Microsoft, argue ‘this is not just another vulnerability’ and risks handing an attacker ‘complete control of your IT’ if IT admins fail to address the issue urgently.
For IT expertise and support, please contact our team today.